Featured
Table of Contents
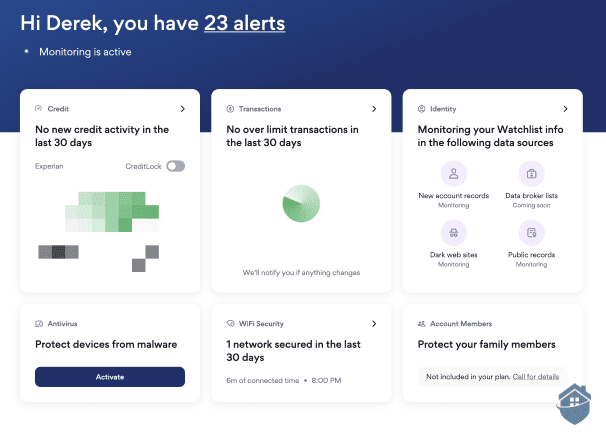
, there are numerous variables to look for, consisting of credit score monitoring, identification tracking, identity burglary healing and insurance and more. They look for signs of identity burglary, such as sudden score movement and unanticipated credit history inquiries. When they see these indicators, they inform the user so they can take action and submit a report.
In addition to that, the plan might have a deductible or various other exemptions or restrictions; most don't cover anybody already covered by occupants or house owners insurance coverage, which is why it's important to constantly check out the fine print - learn more. If your property owners or tenants insurance policy currently covers identity burglary, after that the insurance coverage from your identification burglary protection solution might not apply
The Of Identity Protection Tools
: Lastly, we take an appearance at where the business is based to see what surveillance legislations it drops under. For business based in the USA, they could be required to share consumer data because of the U.S's membership in Five Eyes, Nine Eyes and 14 Eyes. Nonetheless, this will only take place in unusual cases.
Yes, somebody can swipe your identity with your government-issued ID or chauffeur's certificate. (PII) including your full name, home address, date of birth, image or even your signature can be utilized to swipe your identification and target you with phishing scams.
Visualize your vehicle driver's certificate number comes to be jeopardized and falls under the hands of a person that makes duplicates of your ID and after that markets them to crooks. If a criminal obtains caught for any criminal offense with your ID, police can place those charges on your record rather than their own. This situation is really dangerous since it will be testing to verify that you didn't dedicate those criminal activities since an additional person has your ID.
Identity Protection Tools Can Be Fun For Everyone
If someone has your ID, they can utilize your complete name to look you up and discover your e-mail address or telephone number. Once they have ways to call you, someone could send you a phony message about questionable activity in your savings account or a problem with a social networks account.
You can tell if somebody is using your shed or stolen ID for malicious functions by seeing the following: A brand-new loan or line of credit that you did not authorize shows up on your credit rating record, indicating that someone has actually used your ID to dedicate fraudulence You can not log in to your on the internet accounts, suggesting that a person utilized your ID and information connected with your ID to compromise your accounts You stop getting mail, which might be an indicator a person has actually modified the address on your ID to match theirs You begin receiving calls from financial debt collectors regarding financial debt that isn't yours, indicating a person has actually utilized your ID to pose you and been authorized for bank card or loans Your bank cautions you of deceptive task, which means somebody has actually used your ID to withdraw large amounts of money or make unauthorized transactions There are a number of things you ought to do if your ID has actually been lost or swiped, such as reporting the loss or theft to your state's DMV, cold your credit rating and filing a report with the Federal Trade Compensation (FTC).
You need to report your ID as stolen - learn more to the Federal Trade Compensation (FTC), which will certainly utilize the information you give to collaborate with police in examining your identification theft. It is essential to file a record with the FTC asap so the FTC can share your experience with law enforcement to help recoup your identity and use the details from your situation to assist protect others
Our technology group has years of experience with LifeLock, and we have come to be extremely familiar with what they offer. Their most extensive strategy, Ultimate Plus, provides extensive protection and identification burglary resolution services that must cover the requirements of many seniors. We got message, phone, and mobile application signals whenever there was a feasible data violation or misuse of our individual information.
Fascination About Identity Protection Tools
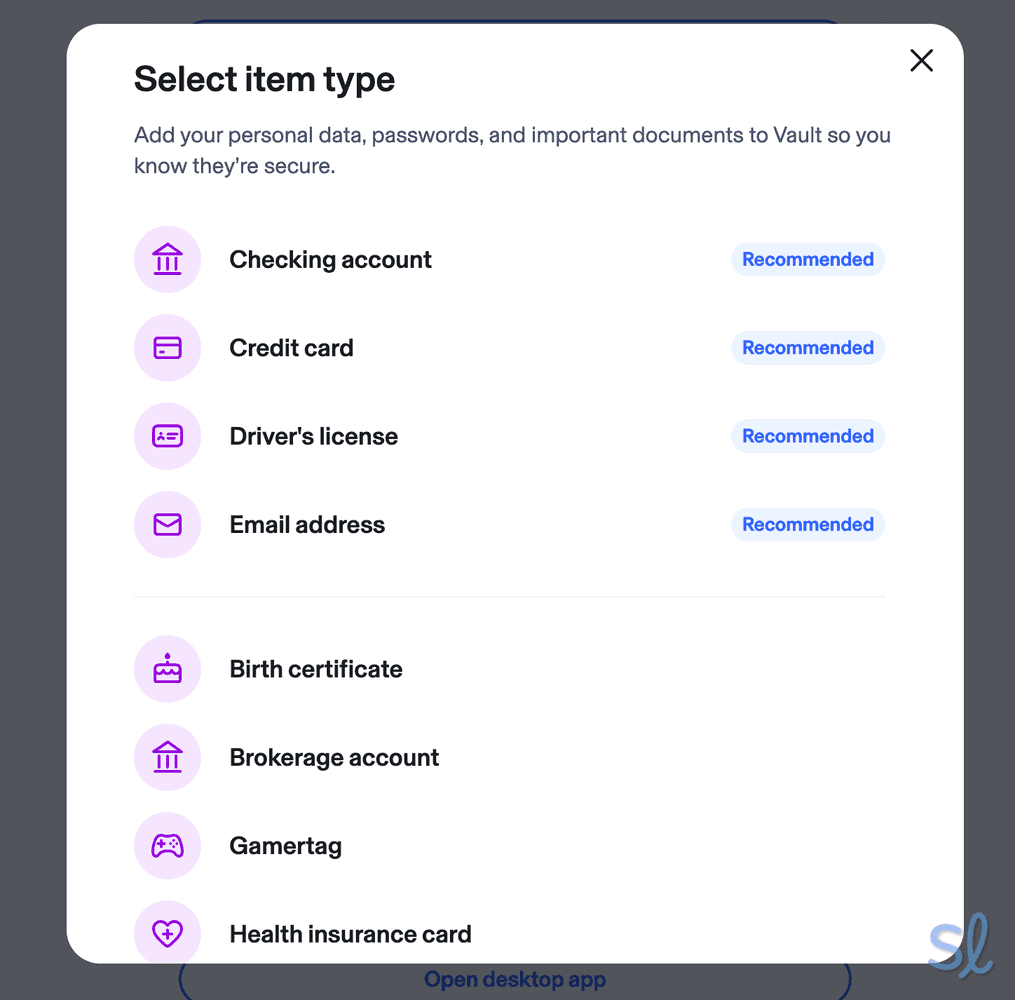
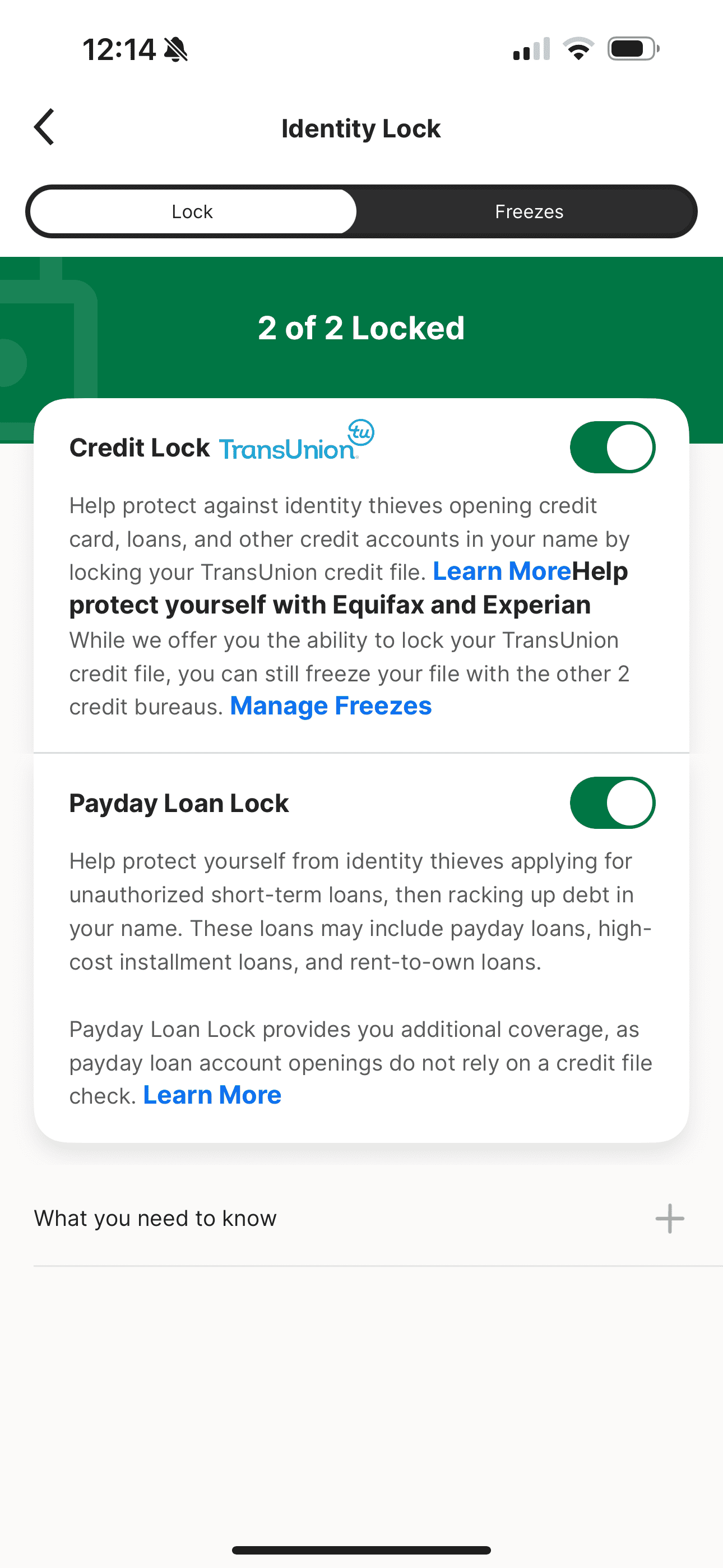
Not all LifeLock plans, however, supply the same level of protection. The Standard plan is somewhat marginal in its offerings, yet you can still stand up to $1.05 million in identification burglary insurance coverage, along with Social Safety and security number, credit report, and economic monitoring. If you're not on a tight spending plan, you can get even more features with one of the costlier plans, such as: Coverage for up to 2 adults As much as $1 million of coverage for legal fees (per adult) Approximately $1 million in personal expenditure reimbursement (per adult) As much as $1 million in taken funds repayment (per grownup) As much as $3 million in complete protection 3 credit history bureau tracking Payday advance lock to stop illegal high-interest fundings Informs for criminal offenses dedicated in your name Social media site monitoring Financial and investment account surveillance Telephone number protection Home title surveillance LifeLock features three identity burglary defense packages varying from $11 - learn more.99 to $69.99 per month for the first year of solution
The discounts go down after the very first year of service. The Standard plan, as an example, sets you back $89.99 for the very first year, and afterwards $124.99 for each year after that. You're still obtaining a price cut by paying yearly, however it's much less from the 2nd year onward. With the addition of anti-virus services and high compensation amounts, however, LifeLock's price is quite reasonable.
Latest Posts
An Unbiased View of Identity Protection Tools
An Unbiased View of Identity Protection Tools
The 20-Second Trick For Identity Protection Tools